What is Network Penetration Testing and How Does it Work?
Cybercrime is a growing problem, especially for businesses. In fact, cybercrime is the fastest-growing type of criminal activity and will cost businesses around $5.2 trillion in the next five years. Although large companies like Facebook and Quest Diagnostics have been in the news for serious data breaches, small businesses should take these threats seriously, too.
43% of small businesses are the target of cyber-attacks. Sometimes, small businesses are specifically targeted because they have smaller IT security budgets, less stringent protocols, and fewer security professionals on staff. Luckily, businesses both big and small can take steps to ensure that sensitive company and client data stays protected from malicious actors.
One method to shore up virtual defenses is hiring ethical hackers to break into your network to probe for weaknesses. Otherwise known as network penetration testing or pen tests, these simulated attacks can help companies address vulnerabilities in a safe manner and prevent criminals from gaining access to your systems.
What is penetration testing?
What types of penetration testing exist?
What is included in a pen test?
What happens after penetration testing?
Why do we need penetration testing?

What is penetration testing?
Penetration testing or ethical hacking allows companies to test their computer systems, web applications, and network by exploring any weak points or security vulnerabilities. These tests can be performed manually or with software.
In some cases, these pen tests are called “white hat attacks” because they’re considered permissible hacking attempts rather than actual cybercriminal intrusions.
The most common cyberattacks against businesses that are not permissible include the following:
- Zero-day exploits: An attack that occurs between the time a security weakness is publicized and when the security upgrade is available.
- SQL injection: A malicious code is installed on a database management software (SQL server).
- Man-in-the-middle attack: A hacker interrupts a transaction between two entities to steal data.
- Phishing: Targets are contacted by SMS, email, or phone by an individual posing as a company or another legitimate institution in order to trick them into providing sensitive information.
- Malware: This can be in the form of viruses, trojans, spyware, and anything else that disrupts the normal functioning of a single device, system, web application, or networ
- Distributed Denial of service (DDoS) attack: The method leveraged most frequently for this attack is a hacker flooding a network with an overwhelming volume of “junk” traffic that paralyzes the system, making it inaccessible for normal users.
Potential consequences of a cyberattack
A cyber attack can negatively impact businesses by causing damage to electronic data which may require expensive fixes. For example, if hackers infiltrate company laptops, business owners may have to invest in new laptops while the compromised devices are being repaired. Companies can also suffer from lost income if a denial of service attack renders your company’s virtual storefront unusable.
Your company may also be vulnerable to security and privacy lawsuits if customer or client data is stolen by a hacker. As a result, clients can sue your business for damages, or take their business elsewhere due to the loss in trust. Hackers may also try to extort you if they obtain sensitive data and may lock certain files or threaten to publicize private information unless you agree to pay a ransom.
And lastly, one of the most serious impacts of a data breach or hack is the damage to your company reputation. If you lose the trust of your customers, employees, shareholders, clients, investors, and anyone else who is involved with your company, you run the risk of losing business. Penetration testing can help prevent these types of worst-case scenarios.

What types of penetration testing exist?
There are several ways to conduct a penetration test and each type of simulated attack can reveal different IT weaknesses that you can take steps to fix after the testing is complete.
White Box Pen Test: During a white box pen test, the testing team is given information about the target network before they begin, such as IP addresses and security protocols.
Covert Pen Test: A covert pen test (or black box testing) is when the tester is given the name of the company that serves as the target. In turn, the IT security team can watch in real-time how an attack would occur.
Double-Blind Pen Test: In this scenario, the IT team has no idea a simulated attack is happening.
External Pen Test: External penetration tests target the assets of a company visible on the internet such as the company website. The goal of this test is to access and steal sensitive data.
Internal Pen Test: An internal pen test means that the hacker has access to an application behind its firewall. While this can simulate the kind of damage a disgruntled employee can do, it can also mimic the effect of an employee’s credentials being stolen due to a phishing attack.
Targeted Pen Test: In a target pen test, the IT team and penetration testing team work side-by-side. It’s also referred to as a “lights turned on” approach because everyone is watching and learning as the test is conducted.
Pen Testing as a Service (PTaaS): This type of pen testing gives your IT security team the resources necessary to conduct and act on the results of continuous pen tests.
What is included in a pen test?
Penetration tests typically involve tools to identify and scan systems for weaknesses and exploitable vulnerabilities. In most cases, network pen testing is the most helpful type of penetration test because it evaluates the strength of the network infrastructure of a business. The test can be conducted on-site or remotely. It’s typically recommended to do both remote and on-site attacks to obtain the most data possible.
Network penetration testing can include DNS attacks, IPS evasion, firewall bypass testing, stateful analysis testing, and firewall configuration testing. Common types of company software analyzed during the testing include Secure Shell (SSH), SQL Server, MySQL, Simple Mail Transfer Protocol (SMTP), File Transfer Protocol, and Microsoft Outlook login pages.
What happens after penetration testing?
Although pen testing in and of itself is critical for companies who want to maintain the highest standards of security, they are not useful if they don’t result in action. The information gathered from a pen test can be used to upgrade security or patch any weak points. Upgrades might include DDoS mitigation (successfully protecting a network from a DDoS attack), new WAF (Web Application Firewall) rules, and rate-limiting (network traffic control), in addition to new security policies.
It’s important to conduct pen tests on a regular basis to ensure that all systems stay secure. Consistent testing means that vulnerabilities are discovered sooner. It’s also a good idea to run a penetration test if any of these situations occur:
- End-user policies are changed
- New security patches are applied
- Company moves to a new office location
- New network infrastructure or applications are added
- Upgrades of modifications are applied to infrastructure or applications
Why do we need penetration testing?
Penetration testing can help companies in a variety of ways, from refreshing security protocols for employees to exploring virtual methods for buttressing network infrastructure.
Manage IT system vulnerabilities
Pen tests show company IT teams where vulnerabilities exist within their cyber-security systems. In turn, businesses can decide where to prioritize bolstering their defenses and where to apply security patches.
Avoid network downtime due to breach
A security breach can be a very serious and expensive problem to fix. Not only do companies need to spend money on IT remediation efforts in the event of a data breach, but they also need to reach out to affected customers. Plus, the resulting legal proceedings can drag out the timeline for resolution for any security problems. Extensive penetration testing can help you avoid that hassle altogether.
Avoid fines by meeting regulatory requirements
Penetration testing helps companies address their compliance standards – or lack thereof. The reports from pen tests may allow businesses to avoid fines for non-compliance and show regulatory bodies evidence of ongoing due diligence through continuous security maintenance.
Educate employees
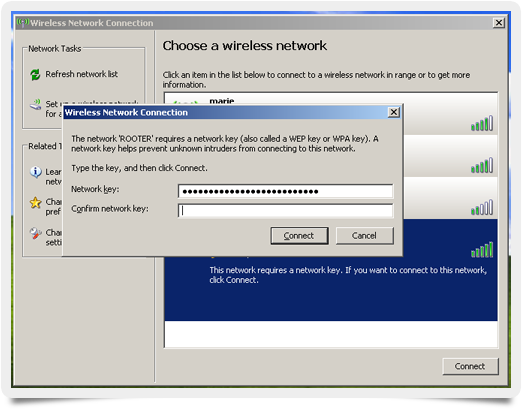
If employees mistakenly left out password information or were the victims of a simulated phishing scheme that caused them to provide sensitive login credentials, a pen test allows the company to reiterate security protocols. Ethical hacking can help your employees understand the importance of protecting their passwords and understanding when to report suspicious emails and other red flags.
Network security for businesses and beyond
Whether you want to learn how to secure your WiFi, explore internet bandwidth hacks, or want to protect your smart devices with UTM for home, Bandwidth Place is here to provide you with the resources and information you need to keep your home network and company network safe.